Infinity: Hacking for Dummies
Probably one of the most intimidating aspects of Infinity is hacking. From the perspective of an outsider, it seems like a needlessly complex system of fiddly rules to roughly approximate what other games would call "magic." Now that I've had a bit more experience with the game, I can gladly say, it's no such thing. The rules are deceptively simple, really being no more than a set of extra long and short orders that you can perform with hacker models. To break it down, we'll be going over the Who/What/When and How of Hacking.
Who can I hack?
In the future world of Infinity, there are many advanced technologies being used in battle. Everything from basic communication gear, to highly sophisticated war machines are all reliant on computers to function, and these computers are vulnerable to being hacked. You can generally think of hacking of having 3 main types of programs, offensive, defensive, and support.
Offensive programs (usually called Claw or Sword) will target enemy Heavy Infantry, Remotes, Tags and other Hackers, with the primary goal of reducing effectiveness or outright destroying the target. Defensive programs (aptly called Shield) are the logical counter to those, offering protection from enemy Hackers, disrupting enemy guided munitions, or even interfering with enemy Combat Jumpers. Support programs (nicknamed Gadget) are the most broad, doing things like assisting your own combat jumpers, boosting the effectiveness of your Remotes, and opening locked doors.
Each hacking program can affect specific unit types, and specifically only if they have the Hackable characteristic. In addition, a hacker can only target units in their Zone of Control (8"), in the Zone of Control of any friendly model with a Repeater, or in the Zone of Control of a friendly deployable repeater. This collective area is referred to as your Hacking Area.
What do I hack with?
Every army in the game (though extremely limited in Ariadna) has access to Hackers, and it will be noted in the model's equipment what type of hacking device they have. Simply put, different types of hacking devices have different programs to choose from. There are 4 types of hacking device:
- Hacking Device - Your bog standard Hacking device, it has a good mixture of offensive, defensive and supporting programs.
- Hacking Device Plus - As it's name implies, it's a regular hacking device, but with a couple more powerful options.
- Defensive Hacking Device - This device sacrifices all the normal offensive programs, as well as some supporting, to gain very powerful defensive programs.
- Assault Hacking Device - Very much the opposite of the defensive hacking device, the Assault hacking device specializes in abilities meant to destroy or disable enemy units.
You can find a complete table of all the hacking programs on the Infinity Wiki page. The columns on the right designate which kind of hacking devices have the associated program. I suggest you check it out, because I'll be referencing it a few times through the article.
When do I hack?
Much like asking "When do I shoot?" the answer is when you spend an order to do so! Some hacking programs are short skills, others are entire orders, and many can be used as an ARO. Hacking in your own turn is simple, spend an order, pick your program and start rolling dice! The target will need to be in range of the Hacker (or a repeater), as expected, and they will be able to ARO, their ARO however might be hampered by the fact that you're out of Line of Sight! There is a special ARO that can be taken against hacking called Reset, which works very similarly to dodge.
Hacking as an ARO however is really fun. If an enemy Heavy Infantry model declares an action within 8" of one of your repeaters, you are allowed to declare an ARO, even without Line of Sight. Because Hackers are able to ARO without line of sight, it makes it very dangerous for hackable enemies to lurk around repeaters.
How do I hack?
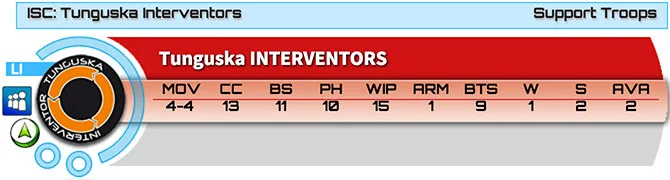
Okay, now the real meat of it all, how do you do it? Using the scenario above, lets pretend we have an enemy Wu Ming who has just activated within 8" of a Fast Panda (which is a Repeater) owned by a very skillful Tunguska Interventor.
| Name | Range | Att. MOD | Opp. MOD | DAM | B | Ammo | Target | Effect | Skill Type | Special |
| Gotcha! (CLAW-1) | Hacking Area | 0 | 0 | 13 | 2 | TAG, HI, REM, Hacker | IMM-1 state | Short/ARO | 2 Turns. |
First, we have the ability itself. Gotcha! has a range limited to the Hacking Area, with no modifiers to either the attacker or opponent's WIP. It has a damage of 13, which means if successfully used, the enemy will take a damage 13 hit against their BTS. If the enemy fails their BTS save, they will suffer the effect Immobilized-1 and it will last for 2 turns as indicated. The Burst of 2 is only usable in the active turn, since this is an ARO, we are restricted to the typical Burst of 1, and Gotcha! can be used against TAGs, Heavy Infantry, Remotes or Hackers. This is all written fairly shorthand in the table, but you can see the text on the Gotcha! program's wiki page.
Now we have the Combatants, an enemy Wu Ming, and your own Tunguska Interventor.
First the Wu Ming declares a Move order with their first short skill, since the model is within 8" of the Repeater, and is Hackable, the Interventor declares a Hacking ARO, even without Line of Sight. The program the Interventor decides to use is called Gotcha!. In response to potentially becoming Immobilized-1 for 2 turns, the Wu Ming declares it's second short skill as a Reset.
The Wu Ming has WIP 13, while the Interventor has an astounding WIP 15. Both players now make their Face-to-Face roll. The Wu Ming rolls a very solid 11, but unfortunately for him, the Interventor scores a 14. Having won the Face-to-Face roll, the Wu Ming must now pass a BTS save. After reducing the damage of the attack by the Wu Ming respectable BTS 3, the Wu Ming must roll an 11 or greater to avoid the attack. If the Wu Ming passes, there will be no ill effects, but if the Wu Ming fails, it will be stuck in Immobilized-1 until the end of the next player's turn!
Things to Remember
There are a few rules that interact with Hacking that are often forgotten, but are incredibly important to know.
- Hacking AROs, like any other ARO is affected by Stealth, so if a model has Stealth and only performs short movement skills near a Repeater, the hacker will not get to ARO unless it also has Line of Sight.
- Hacking can be used to make a Surprise Shot! That's right, your camouflaged hacker can pop up on the active turn and attempt to hack the enemy, who will suffer a -3 Mod on any face to face roll against the hacker that round.
- It may be tempting to put a Hacker in a Fireteam, which would help them move up the board to use their abilities, be careful though because if you use any of the Hacking Programs that are Entire Orders, it will force the Hacker out of the Fireteam. That said, you can actually perform any of the Short Skill hacking programs while in a fireteam, though you will not any bonuses for being in one.

If you have any of your own tips and suggestions for our new hackers, I'd love to hear it, please leave them in the comments!